Enjoy fast, free delivery, exclusive deals, and award-winning movies & TV shows with Prime
Try Prime
and start saving today with fast, free delivery
Amazon Prime includes:
Fast, FREE Delivery is available to Prime members. To join, select "Try Amazon Prime and start saving today with Fast, FREE Delivery" below the Add to Cart button.
Amazon Prime members enjoy:- Cardmembers earn 5% Back at Amazon.com with a Prime Credit Card.
- Unlimited Free Two-Day Delivery
- Streaming of thousands of movies and TV shows with limited ads on Prime Video.
- A Kindle book to borrow for free each month - with no due dates
- Listen to over 2 million songs and hundreds of playlists
- Unlimited photo storage with anywhere access
Important: Your credit card will NOT be charged when you start your free trial or if you cancel during the trial period. If you're happy with Amazon Prime, do nothing. At the end of the free trial, your membership will automatically upgrade to a monthly membership.
Buy new:
-22% $17.09$17.09
Ships from: Amazon.com Sold by: Amazon.com
Save with Used - Good
$11.46$11.46
Ships from: Amazon Sold by: Steals Depot
Download the free Kindle app and start reading Kindle books instantly on your smartphone, tablet, or computer - no Kindle device required.
Read instantly on your browser with Kindle for Web.
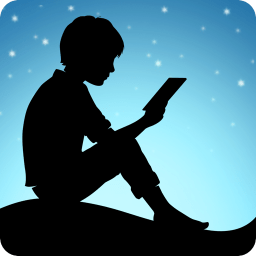
Using your mobile phone camera - scan the code below and download the Kindle app.
OK
 Audible sample Sample
Audible sample Sample 


The Art of Deception: Controlling the Human Element of Security Paperback – October 17, 2003
Explore your book, then jump right back to where you left off with Page Flip.
View high quality images that let you zoom in to take a closer look.
Enjoy features only possible in digital – start reading right away, carry your library with you, adjust the font, create shareable notes and highlights, and more.
Discover additional details about the events, people, and places in your book, with Wikipedia integration.
Purchase options and add-ons
Obwohl die meisten Unternehmen die neuesten Sicherheitssysteme installieren, ignorieren sie doch meist die Gefahr aus den eigenen Reihen.
"The Art of Deception" ist das erste Buch, das sich ausschließlich auf "Social Engineering", d.h., den menschlichen Faktor im Rahmen der Sicherheit konzentriert. Hierbei geht es darum, durch Ausnutzen menschlicher Schwächen, jene Informationen (z.B. Passwörter) zu erhalten, die Unbefugten den Zugang zu (sensiblen) Systemen und Daten erleichtern.
Autor Kevin Mitnick vermittelt hier seine Insidererfahrungen und erläutert die Techniken, mit deren Hilfe sich auch die stärksten Sicherheitsbarrieren überwinden lassen.
Mitnick ist einer der angesehensten Experten auf dem Gebiet des Sicherheitsbetrugs. Er ist bei Hackern ebenso bekannt wie bei Sicherheitsprofis.
Coautor William Simon ist ein Bestsellerautor, der bereits über 20 Bücher veröffentlicht hat; er wurde u.a. mit dem Global Business Book Award ausgezeichnet.
"The Art of Deception" - die ultimative Lektüre im Zeitalter des Cyberterrorismus.
- Print length368 pages
- LanguageEnglish
- PublisherJohn Wiley & Sons Inc
- Publication dateOctober 17, 2003
- Dimensions6 x 1 x 0 inches
- ISBN-10076454280X
- ISBN-13978-0764542800
Books with Buzz
Discover the latest buzz-worthy books, from mysteries and romance to humor and nonfiction. Explore more
Frequently bought together
More items to explore
Editorial Reviews
Review
"...a lot of interesting cautionary tales..." (New Scientist, January 2004)
Product details
- Publisher : John Wiley & Sons Inc; 1st edition (October 17, 2003)
- Language : English
- Paperback : 368 pages
- ISBN-10 : 076454280X
- ISBN-13 : 978-0764542800
- Item Weight : 15.2 ounces
- Dimensions : 6 x 1 x 0 inches
- Best Sellers Rank: #34,088 in Books (See Top 100 in Books)
- #11 in Computer Hacking
- #13 in CompTIA Certification Guides
- #16 in Information Management (Books)
- Customer Reviews:
About the authors

William L. Simon is the author or co-author of more than 30 books, including numerous New York Times, national, and international bestsellers. Born in Washington, DC, he holds two degrees from Cornell University, and has been a freelance writer ever since -- first as a writer of documentaries, corporate, and informational films, then as a book author. He is a member of the Writers Guild of America, West, and now lives in Los Angeles.
Customer reviews
Customer Reviews, including Product Star Ratings help customers to learn more about the product and decide whether it is the right product for them.
To calculate the overall star rating and percentage breakdown by star, we don’t use a simple average. Instead, our system considers things like how recent a review is and if the reviewer bought the item on Amazon. It also analyzed reviews to verify trustworthiness.
Learn more how customers reviews work on AmazonReviews with images
-
Top reviews
Top reviews from the United States
There was a problem filtering reviews right now. Please try again later.
Our tendency to be helpful.
Our tendency to let someone new come into our lives
Etc,..
I will be honest, after spending 13 years in financial and marketing industry and reading 1000s of books and having 1000s of experiences I promise if someone wants to set me up they probably can.
It's really hard to get away from a good setup.
One thing that helped me all these years is that at the end of the day I ask myself two questions. This is a routine I do every day and been doing it for almost 10 years now.
1. Did I try to help a stranger or someone I know today? If yes, then what was the context.
2. Did someone came in my life trying to do good things for me out of blue? (This can be a friend that randomly texts you on FB or emails you after ages.)
All the firewalls and software can't prevent a social engineer from getting in if he/she knows justs how to act and/or what to say to get what they want. Reading the scenarios really opened my eyes. Theres a scenario where a social engineer pretended to be a manager of a video store. After enough talking to another employee at another branch, the social engineer was able to get enough information to obtain the credit card # of someone who owed money to the client the social engineer was hired by.
In reading the scenarios, I'd seen examples where I'd asked for the type of information described for perfectly legitimate reasons. I'd never imagined how someone could take just 1 or 2 pieces of information and create chaos for a person or a company. If you're in the IT industry, or work in any kind of customer service, you really need to pick up this book. This book doesn't bash people for being as helpful as they can be (team player, etc). He's just saying to be more aware of what's going on and when giving out any kind of information, being a little cautious doesn't hurt. As humans, we're not perfect to begin with, but a little awareness will make it just a little harder for that social engineer to get what they want.
The techniques that the author points out on how easy it is to simply ask for information and get it was just too much to pass up. I've tied it within my own audit department to see just how susceptible we are...I still can't believe how open people were to provide me information not knowing who I was.
Everyone should read this book...there are parts that are a little too much for some people but the scenarios that he walks you through are so thorough that you'd swear you've had that conversation before.
'Social Engineering' made simple...maybe that should be the name of this book. I will have to admit that I'm more paranoid than I have ever been before but I guess that is a good trait to have in an auditor.
This book focuses on the human element of computer security. Reminding us that even the most sophisticated high-tech security systems can be rendered worthless if the people running them are not sufficiently vigilant, Mitnick goes on to point out the myriad ways in which human carelessness can contribute to security breaches. An experienced con artist who is well-versed in social engineering techniques can often do far more damage by manipulating people to provide information they shouldn't than by relying on technologically sophisticated hacking methods.
The book is interesting for the most part, though it would have benefited from a 25% reduction in length, and there are some annoying stylistic tics. Throughout the first 14 chapters, each of which reviews a particular type of `con' used by hackers/social engineers to breach computer security, the chapter setup follows the same schema:
(i) an anecdote or vignette, involving fictitious characters but based on actual events, which lays out the deception as it unfolds, following it through to the successful breach (ii) analysis of the `con', focusing specifically on the mistakes or behaviors (at the individual and at the organizational level) which allowed it to succeed (iii) discussion of the changes that would be needed to stop the con from succeeding (e.g. behavior of individual employees, corporate policies and procedures, computer software and hardware). This is actually a pretty decent way to make the points Mitnick wants to get across - starting out with a concrete example of how things go wrong gets attention and motivates the reader to read on to figure out the solution.
One feature of the book which was meant to be helpful started to annoy me by about the third chapter. Interspersed throughout each chapter, the authors insert highlighted textboxes of two types: `lingo' - repeating the definition of a concept already adequately defined in the text, or `mitnick messages' - which seemed superfluous, and a little condescending, as they generally repeated what was already obvious. In general, this is not a book you will read for the delights of its prose style (after successfully gaining access to a cache of hidden documents, one hacker is described as spending his evening gleefully "pouring over" the documents); however, the prose is serviceable, managing to avoid lapses into the dreaded corpspeak, for the most part.
For some readers, the most useful part of the book may be its final two chapters. Here the authors lay out, in considerable detail, outlines for recommended corporate information security policies, and an associated training program on information security awareness. Though I am no expert in these areas, the outlines strike me as being commendably thorough - complete enough that they could be fleshed out without too much difficulty to generate a comprehensive set of policies and procedures.
Despite some redundancy, and occasional infelicities of style, this book seemed to me to be interesting, and likely to be practically useful.